In today’s interconnected world, safeguarding your business from cyber threats is not just an option it’s a necessity. At Elysian Communication, we understand the critical importance of a robust security posture. That’s why we offer comprehensive IT Security Audit Services designed to identify vulnerabilities, strengthen your defenses, and ensure your digital assets are protected.
Founded in 2015, Elysian Communication Private Limited has been at the forefront of providing cutting-edge IT and network security solutions. With over 20 years of collective experience in the IT sector, our team brings unparalleled expertise to businesses in Madurai, Tamil Nadu, and beyond. Our commitment is to help you achieve digital transformation and growth securely.
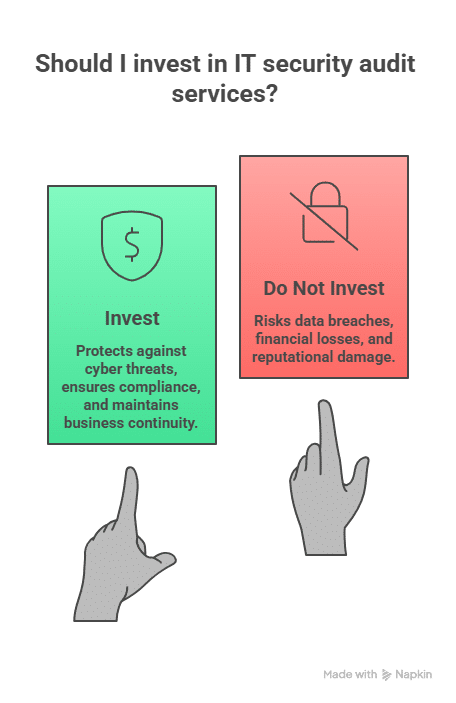
Why IT security audit services are essential for your business
Cyber threats are constantly evolving, making a one-time security check insufficient. An IT security audit is a systematic evaluation of your organization’s information system. It identifies security weaknesses, evaluates compliance with security policies, and determines the effectiveness of current security measures. Think of it as a thorough health check for your digital infrastructure.
Without regular IT security audit services, your business could be exposed to data breaches, financial losses, reputational damage, and operational disruptions. We help bridge the gap between your current security posture and the robust defenses required in today’s threat landscape.
Our approach to IT security audit services
At Elysian Communication, our IT security audit services are not just about finding flaws; they’re about providing actionable insights and strategic recommendations. We employ a multi-layered approach, leveraging our deep expertise in network security & vulnerability audits, penetration testing, and web & application security testing.
Understanding your unique security landscape
Every business is unique, with its own set of challenges and compliance requirements. Our process begins with a detailed assessment of your existing IT infrastructure, policies, and procedures. This initial phase helps us understand your specific needs and tailor our IT security audit services accordingly. We look at everything from your network architecture to your employee security awareness.
Comprehensive vulnerability assessments
A critical component of our IT security audit services is identifying potential weaknesses that attackers could exploit. We perform in-depth vulnerability assessments to scan for configuration errors, outdated software, and other security gaps. This proactive scanning helps us pinpoint where your defenses might be weakest before they can be compromised.
Our vulnerability scans cover:
- Network devices and infrastructure
- Server configurations
- Applications and software
- Database security
Rigorous penetration testing (pentesting)
While vulnerability assessments identify potential weaknesses, penetration testing actively simulates a real-world cyber attack to exploit those vulnerabilities. This hands-on approach provides a true understanding of how your systems would fare against a malicious actor. Our ethical hackers attempt to breach your defenses, mimicking the tactics of sophisticated cybercriminals.
This includes:
- External penetration testing (from the internet)
- Internal penetration testing (from within your network)
- Web application penetration testing
- Mobile application penetration testing
You can learn more about how we specialize in protecting your online presence by visiting our page on cybersecurity services.
Web and application security testing
Many cyber attacks target web applications, making their security paramount. Our IT security audit services include thorough testing of your web applications to uncover vulnerabilities such as SQL injection, cross-site scripting (XSS), insecure direct object references, and more. We help ensure your customer data and business operations are safe from application-layer threats.
Compliance and regulatory adherence
For many industries, maintaining compliance with various regulations (e.g., GDPR, HIPAA, ISO 27001) is non-negotiable. Our IT security audit services assess your adherence to these standards, helping you avoid costly fines and reputational damage. We provide recommendations to close compliance gaps and implement best practices.
Key benefits of our IT security audit services
Investing in regular IT security audit services with Elysian Communication offers numerous advantages for your business:
| Benefit | Description |
| Early Threat Detection | Identify vulnerabilities before exploitation. |
| Enhanced Security | Strengthen defenses against cyber attacks. |
| Compliance Assurance | Meet regulatory and industry standards. |
| Risk Reduction | Minimize impact of potential breaches. |
| Optimized Investments | Direct security spending effectively. |
| Business Continuity | Ensure uninterrupted operations. |
| Reputation Protection | Maintain trust with customers and partners. |
Proactive identification of vulnerabilities
One of the most significant benefits of our IT security audit services is the ability to proactively identify weaknesses in your systems. By discovering and addressing these vulnerabilities before they are exploited, we help you prevent security incidents, saving you time, money, and stress. Our typical malware investigation duration is a few hours to a few days, but preventing an incident altogether is always the best approach.
Strengthening your overall security posture
Our comprehensive audits provide a clear assessment of your technical defenses, pinpointing areas that need improvement. We don’t just tell you what’s wrong; we provide detailed, actionable recommendations to improve the efficiency of your cybersecurity controls. This systematic approach ensures continuous improvement in your security posture.
Ensuring compliance and reducing risk
Navigating the complex landscape of security regulations can be challenging. Our IT security audit services help ensure your business adheres to relevant industry standards and data protection laws. By reducing your compliance risks, we help safeguard your organization from legal penalties and enhance your credibility. We also offer specialized cloud security services to ensure your cloud environments meet crucial compliance standards.
Beyond the audit: Our holistic security solutions
An IT security audit is just one piece of the puzzle. At Elysian Communication, we believe in providing end-to-end security solutions. After identifying vulnerabilities, we work with you to implement robust countermeasures and build a resilient security framework.
Managed IT security services
Once your audit is complete and recommendations are implemented, we can continue to support your security needs through our managed IT security services. This proactive approach includes continuous monitoring, threat detection, and rapid incident response, ensuring your business stays protected 24/7. With our 24/7 managed IT support, we provide continuous operational excellence.
Advanced network security solutions
Our expertise extends to designing and implementing multi-layered network security frameworks. This includes firewall installation and configuration, intrusion detection/prevention systems, and secure network architecture design. We ensure your network is robust and capable of defending against modern threats.
Our Founder and Chairman, Sundaresh Kamaraj, with over 26 years in the IT sector, has instilled a philosophy of holistic security and innovation that drives all our services. His specializations in business analysis, strategic development, and artificial intelligence and data science reinforce our ability to offer future-ready solutions.

Why choose Elysian Communication for IT security audit services?
When it comes to protecting your business, experience and expertise matter. Elysian Communication stands out as a trusted partner for IT security audit services for several reasons:
- Deep Industry Expertise: With over 20 years of experience in the IT sector and our skilled team, we bring a wealth of knowledge to every engagement.
- Comprehensive Solutions: From network security to cloud solutions and managed support, we offer a full suite of services to meet your evolving needs.
- Client-Centric Approach: We pride ourselves on understanding your unique challenges and delivering tailored solutions that truly work for your business.
- Proven Track Record: Since 2015, we’ve successfully assisted numerous businesses in achieving digital transformation and growth, earning over 15 awards along the way.
- Local Presence, Global Standards: While based in Madurai, Tamil Nadu, we adhere to global best practices, bringing world-class IT security audit services to your doorstep.
We are a company that focuses on client success above all else. Our team, though 25 strong, operates with the agility and dedication of a startup, backed by the extensive experience of leaders like Sundaresh Kamaraj.
Ready to secure your digital future?
Don’t wait for a security incident to expose your vulnerabilities. Proactive IT security audit services are your first line of defense. Let Elysian Communication help you understand your current security posture, identify potential threats, and build a stronger, more resilient defense system.
We invite you to reach out to us for a consultation. Our team is ready to discuss how our tailored IT security audit services can benefit your organization. Secure your peace of mind and accelerate your digital journey with a trusted partner.
You can learn more about our general IT auditing capabilities on our IT auditing page, or specifically about IT auditing in Madurai.
Benefits of Choosing Elysian Communication Private Limited
Partnering with Elysian Communication Private Limited for IT Security Audit Services offers:
- Expert cybersecurity professionals
- Comprehensive risk assessments
- Compliance-focused audits
- Customized security solutions
- Continuous monitoring and support
Our IT Security Audit Services help businesses stay ahead of evolving cyber threats.
Future Trends in IT Security Audit Services
The future of IT Security Audit Services is rapidly evolving as organizations adopt advanced technologies and face increasingly sophisticated cyber threats. Modern security audits are no longer limited to periodic reviews; they are becoming continuous, intelligence-driven processes that help businesses stay resilient, compliant, and competitive in a digital-first world.
Key Trends:
- One of the most significant trends is AI-driven threat detection, where artificial intelligence and machine learning analyze vast volumes of security data to identify anomalies, predict potential breaches, and respond to threats in real time. This proactive approach enhances the effectiveness of IT Security Audit Services by reducing response time and minimizing risk exposure.
- Another key trend is the growing importance of cloud security audits. As businesses migrate workloads to cloud platforms, IT Security Audit Services must evaluate cloud configurations, identity and access management, data protection controls, and compliance with global standards. Regular cloud audits ensure secure adoption of cloud technologies while maintaining operational efficiency.
- The adoption of Zero Trust architecture is also transforming IT Security Audit Services. This model operates on the principle of “never trust, always verify,” requiring strict identity verification for every user and device accessing the network. Security audits now assess Zero Trust policies, micro-segmentation, and continuous authentication mechanisms to ensure robust protection against insider and external threats.
- Additionally, automated compliance monitoring is reshaping the audit landscape. Automation tools continuously track regulatory requirements, generate compliance reports, and detect policy violations. This reduces manual effort, improves accuracy, and ensures organizations remain compliant with standards such as ISO, GDPR, and industry-specific regulations.
Businesses that adopt modern IT Security Audit Services benefit from improved risk management, stronger data protection, regulatory compliance, and enhanced customer trust. These advantages ultimately provide a competitive edge in today’s cybersecurity-driven marketplace.
Common Challenges in IT Security Audits
While IT Security Audit Services are essential, organizations often face challenges such as:
- Lack of internal expertise
- Budget constraints
- Complex IT environments
- Rapidly evolving threats
Professional IT Security Audit Services from Elysian Communication Private Limited address these challenges effectively.
Frequently asked questions about IT security audit services
What is an IT security audit and why is it important for my business?
An IT security audit is a thorough examination of your organization’s IT infrastructure, policies, and practices. Its primary goal is to identify security weaknesses, assess compliance with existing policies, and evaluate the effectiveness of your protective measures. It’s crucial because it helps you proactively uncover vulnerabilities that could lead to data breaches, financial losses, or reputational damage, ensuring your business stays secure and compliant.
How often should my business undergo IT security audit services?
The frequency of IT security audit services depends on several factors, including your industry’s compliance requirements, the volume and sensitivity of your data, and the rate at which your IT environment changes. Generally, we recommend at least an annual comprehensive audit. However, for businesses handling highly sensitive data or operating in rapidly changing digital landscapes, more frequent audits (e.g., quarterly or semi-annually) or continuous monitoring might be necessary.
What types of issues do IT security audit services typically uncover?
Our IT security audit services can uncover a wide range of issues. These often include:
Outdated software or unpatched systems
Weak passwords or poor access control policies
Network misconfigurations that create open access points
Vulnerabilities in web applications (e.g., SQL injection, XSS)
Lack of proper data encryption or backup strategies
Employee security awareness gaps
Non-compliance with industry regulations (e.g., ISO 27001, GDPR)
By identifying these, we help you prioritize and remediate them effectively.
Can Elysian Communication help with post-audit remediation?
Absolutely. Our IT security audit services don’t end with a report. We believe in providing holistic support. Once the audit is complete and vulnerabilities are identified, our team can work with you to plan and implement the necessary remediation steps. This includes advising on best practices, assisting with system configurations, deployment of new security technologies, and even providing ongoing IT services in Madurai for continuous improvement. Our aim is to ensure your security posture is not just assessed but also continuously strengthened.
What is the difference between a vulnerability assessment and penetration testing in IT security audit services?
Both are critical components of IT security audit services but serve different purposes. A vulnerability assessment (VA) is like an X-ray, scanning your systems for known weaknesses and providing a list of potential vulnerabilities. It identifies “what could be attacked.” Penetration testing (PT) is like a simulated attack. Our ethical hackers actively try to exploit those identified vulnerabilities to see if they can gain unauthorized access, assess the extent of potential damage, and test your response capabilities. It determines “what can actually be attacked.
How long does an IT security audit take and what is the process?
The duration of an IT security audit varies significantly based on the size and complexity of your IT infrastructure. It can range from a few days for smaller assessments to several weeks for large enterprises. Our typical process involves:
Scope Definition: Understanding your assets, systems, and objectives.
Information Gathering: Collecting data about your network, applications, and security policies.
Vulnerability Analysis: Using automated tools and manual techniques to identify weaknesses.
Penetration Testing (Optional/Included): Simulating attacks to exploit identified vulnerabilities.
Reporting: Providing a detailed report of findings, risks, and actionable recommendations.
Remediation Support: Assisting your team in implementing fixes and improving security.
For more specific details, please contact us directly.
What makes Elysian Communication’s IT security audit services unique?
Elysian Communication brings a unique blend of deep experience, comprehensive solutions, and a client-focused approach. Many of our peers have great services and similar offerings, but we believe our differentiators are:
Expert Leadership: Led by Sundaresh Kamaraj, with over 26 years of IT experience, our services are grounded in profound industry knowledge.
Holistic Approach: We offer end-to-end solutions, from audit and assessment to implementation and managed security.
Local Expertise with Global Standards: We understand the unique challenges of businesses in Madurai and across India, while adhering to international best practices.
Commitment to Innovation: We continuously deploy advanced technologies and strategies to counter the latest cyber threats, ensuring future-ready systems.
Proven Success: Over 15 awards and countless satisfied clients since 2015 speak to our dedication and effectiveness.
We are a trusted tech partner dedicated to accelerating your digital journey securely.
Conclusion
In an era where cyber threats are increasingly sophisticated, IT Security Audit Services are no longer optional — they are essential. A well-executed audit helps businesses detect vulnerabilities, strengthen defenses, ensure compliance, and build customer trust.
By following these 10 essential tips, organizations can maximize the effectiveness of their IT Security Audit Services and stay ahead of cyber risks.
Elysian Communication Private Limited stands as a trusted partner, delivering expert IT Security Audit Services tailored to modern business needs. Investing in professional IT Security Audit Services today ensures a secure, resilient, and future-ready organization.





